HTTP Toolkit has released version 1.26.0, enhancing its capabilities for intercepting HTTP and HTTPS traffic seamlessly from a wide array of clients, including popular web browsers like Chrome and Firefox, various command-line tools, and back-end programming languages such as Node.js, Python, and Ruby. This tool serves as an HTTP(S) proxy, effectively functioning with standard HTTP requests across multiple platforms that may lack direct integration.
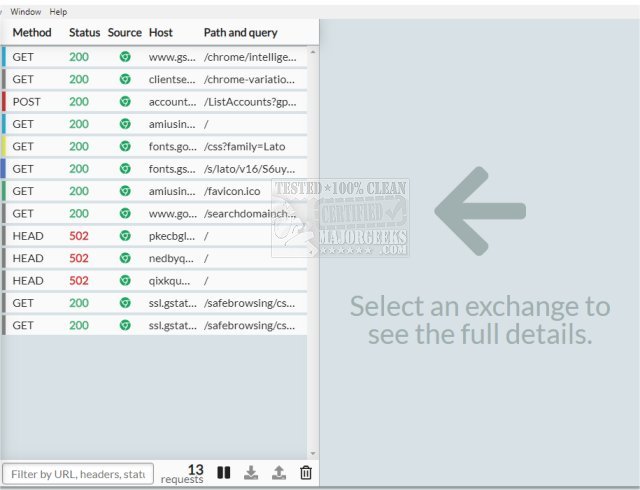
One of the standout features of HTTP Toolkit is its ability to sift through incoming traffic, allowing users to sort by content type, status, and source. It also includes robust search options based on URL, status, and headers to facilitate the identification of relevant messages. With inline documentation and explanations sourced from MDN, users can quickly analyze the details of each request or response, including URL, status, headers, and body. The integration of the Monaco editor from Visual Studio Code enables users to perform detailed inspections of message bodies, which are automatically highlighted and formatted for various data types including JSON, HTML, and hex.
In addition to these features, HTTP Toolkit allows users to pause and edit live HTTP traffic by matching requests. Users can modify target URLs, methods, headers, or bodies as needed and can manually respond to requests in real-time or intercept and modify responses before they return to the client. This functionality includes the ability to step through requests one at a time or create mock endpoints and errors for testing purposes.
Key Features of HTTP Toolkit:
- Cross-platform compatibility (Linux/Mac/Windows)
- Support for all interception integrations
- Essential tools for HTTP debugging
- Manual HTTP mocking and rewriting capabilities
For users experiencing common network issues, the toolkit also provides guidance on troubleshooting such as fixing unidentified networks on Windows, flushing the DNS cache, resetting TCP/IP settings, and using the ping command effectively.
As HTTP Toolkit continues to evolve, it remains a powerful resource for developers and testers looking to gain better insights and control over their HTTP traffic, making web development and debugging more efficient and effective
One of the standout features of HTTP Toolkit is its ability to sift through incoming traffic, allowing users to sort by content type, status, and source. It also includes robust search options based on URL, status, and headers to facilitate the identification of relevant messages. With inline documentation and explanations sourced from MDN, users can quickly analyze the details of each request or response, including URL, status, headers, and body. The integration of the Monaco editor from Visual Studio Code enables users to perform detailed inspections of message bodies, which are automatically highlighted and formatted for various data types including JSON, HTML, and hex.
In addition to these features, HTTP Toolkit allows users to pause and edit live HTTP traffic by matching requests. Users can modify target URLs, methods, headers, or bodies as needed and can manually respond to requests in real-time or intercept and modify responses before they return to the client. This functionality includes the ability to step through requests one at a time or create mock endpoints and errors for testing purposes.
Key Features of HTTP Toolkit:
- Cross-platform compatibility (Linux/Mac/Windows)
- Support for all interception integrations
- Essential tools for HTTP debugging
- Manual HTTP mocking and rewriting capabilities
For users experiencing common network issues, the toolkit also provides guidance on troubleshooting such as fixing unidentified networks on Windows, flushing the DNS cache, resetting TCP/IP settings, and using the ping command effectively.
As HTTP Toolkit continues to evolve, it remains a powerful resource for developers and testers looking to gain better insights and control over their HTTP traffic, making web development and debugging more efficient and effective
HTTP Toolkit 1.26.0 released
HTTP Toolkit offers automatic interception of HTTP and HTTPS traffic from most clients, including web browsers like Chrome and Firefox, almost all CLI tools, and back-end languages (Node.js, Python, Ruby, and more).