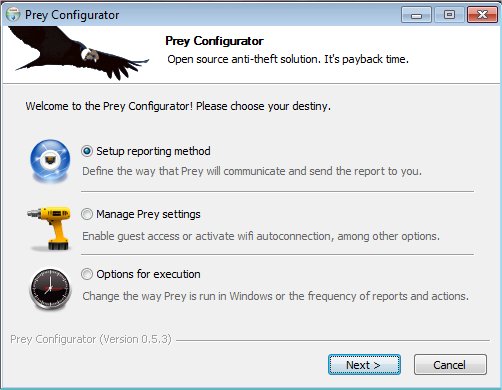
Prey version 1.13.28 has been released, enhancing its functionality as a surveillance tool that helps users track their phones and laptops. This application is designed to assist in locating devices if they are lost or stolen. The setup is straightforward: users install a small agent on their device, which remains inactive until it receives a remote signal via the Internet or SMS. This signal can prompt the device to provide valuable information about its location, hardware, and network status, in addition to enabling various remote actions.
Key features of Prey include the ability to protect up to three devices and generate Theft Evidence Reports, with a limit of 20 reports per device. Users can establish one Control Zone for basic security measures, receive evidence reports at intervals of either 10 or 20 minutes, and access features like location history, an anti-mute alarm, remote screen lock, and customizable on-screen messages. Additionally, Prey offers a camouflage mode to make it less noticeable to potential thieves, a log for hardware changes, an activity log, and two-factor authentication (2FA) for enhanced security.
In summary, Prey provides a robust solution for device tracking and security, making it a valuable tool for safeguarding personal electronics. Users can set up protective measures in just three steps to effectively lock down and protect their laptops or phones, ensuring peace of mind in the event of loss or theft. As technology evolves, it is likely that Prey will continue to update its features to adapt to new security challenges and user needs
Key features of Prey include the ability to protect up to three devices and generate Theft Evidence Reports, with a limit of 20 reports per device. Users can establish one Control Zone for basic security measures, receive evidence reports at intervals of either 10 or 20 minutes, and access features like location history, an anti-mute alarm, remote screen lock, and customizable on-screen messages. Additionally, Prey offers a camouflage mode to make it less noticeable to potential thieves, a log for hardware changes, an activity log, and two-factor authentication (2FA) for enhanced security.
In summary, Prey provides a robust solution for device tracking and security, making it a valuable tool for safeguarding personal electronics. Users can set up protective measures in just three steps to effectively lock down and protect their laptops or phones, ensuring peace of mind in the event of loss or theft. As technology evolves, it is likely that Prey will continue to update its features to adapt to new security challenges and user needs
Prey 1.13.28 released
Prey is a useful surveillance tool that lets you keep track of your phone or laptop at all times and will help you find it if it ever gets lost or stolen.